Today Microsoft announced a new open-source initiative, SimuLand, to help security researchers deploy lab environments that reproduce well-known techniques used in attack scenarios.
Participants can use the labs to test the effectiveness of Microsoft 365 Defender, Azure Defender, and Azure Sentinel detections. The simulation steps are mapped to detection queries and alerts to the aforementioned technologies.
Threat research will be extended after each simulation exercise through the use of elementary and forensic artefacts generated after each scenario. Roberto Rodriguez, a threat researcher at MSTIC R&D wrote in a blog post:
“Our goal is to have SimuLand integrated with threat research methodologies where dynamic analysis is applied to end-to-end simulation scenarios.”
SimuLand will identify mitigations and attacker paths by documenting preconditions, expedite the design and deployment of threat research lab environments. It will stay up to date on the latest techniques that are used by attackers.
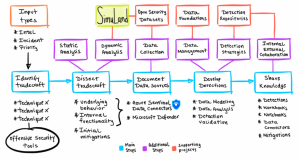
Map of threat research methodologies. Photo Credits: Microsoft
The initiative offers lab guides to prepare and deploy the lab environment and to execute the end-to-end simulation exercise. It stems from the open-source projects Azure Sentinel2Go and Blacksmith from the Open Threat Research (OTR) community. The labs replicate either hybrid cross-domain or cloud environments depending on the simulation.
Every simulation plan provided through the project is research-based and broken down into attacker actions mapped to the MITRE ATT&CK framework. The goal of the simulate and detect component is to summarize the steps used by a threat actor to accomplish a specific object and allow security researchers to get familiarized with the attacker behaviour at a high level.
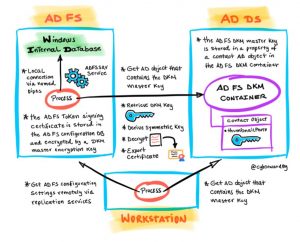
Example of exporting token signing certificate from the federation server. Photo Credits: Microsoft
Microsoft said it’s working to expand the project by possibly adding an A data model to document the simulation steps, a CI/CD pipeline with Azure DevOp, the automation of attack actions and more.
Last month, the Microsoft 365 Defender Research team also released an open-source cyberattack simulator dubbed CyberBattleSim. This simulator allows creating simulated network environments that model how AI-controlled cyber agents spread through a network after its initial compromise.








